While scrolling through Reddit, I found this post from a user in r/Antiscamph, who shared an experience involving a call they received on Google Meet. The caller claimed to be from PhilSys and said the victim's National ID needed replacement. The victim mentioned they were still a bit sleepy at the time and allowed screen sharing, which enabled the threat actor to direct them to a link that looked like the eGovPH site and attempted to social engineer them into downloading an APK and granting admin permissions. The victim got an inkling of what was about to happen and ended the call, which was the right move in this scenario.
I looked into the matter and this is not just your typical phishing campaign. It is a threat campaign that uses social engineering to trick victims into installing a custom crafted malicious APK designed for credential harvesting. The link sent during the call pointed to https://egov.ncbrgo.cc/. The page visually resembles the eGovPH website, but upon further inspection, there are indicators suggesting the site may have been created with the help of an LLM. For example, the "Download on the App Store" option triggers a fake system upgrade message instead of redirecting to the actual App Store.
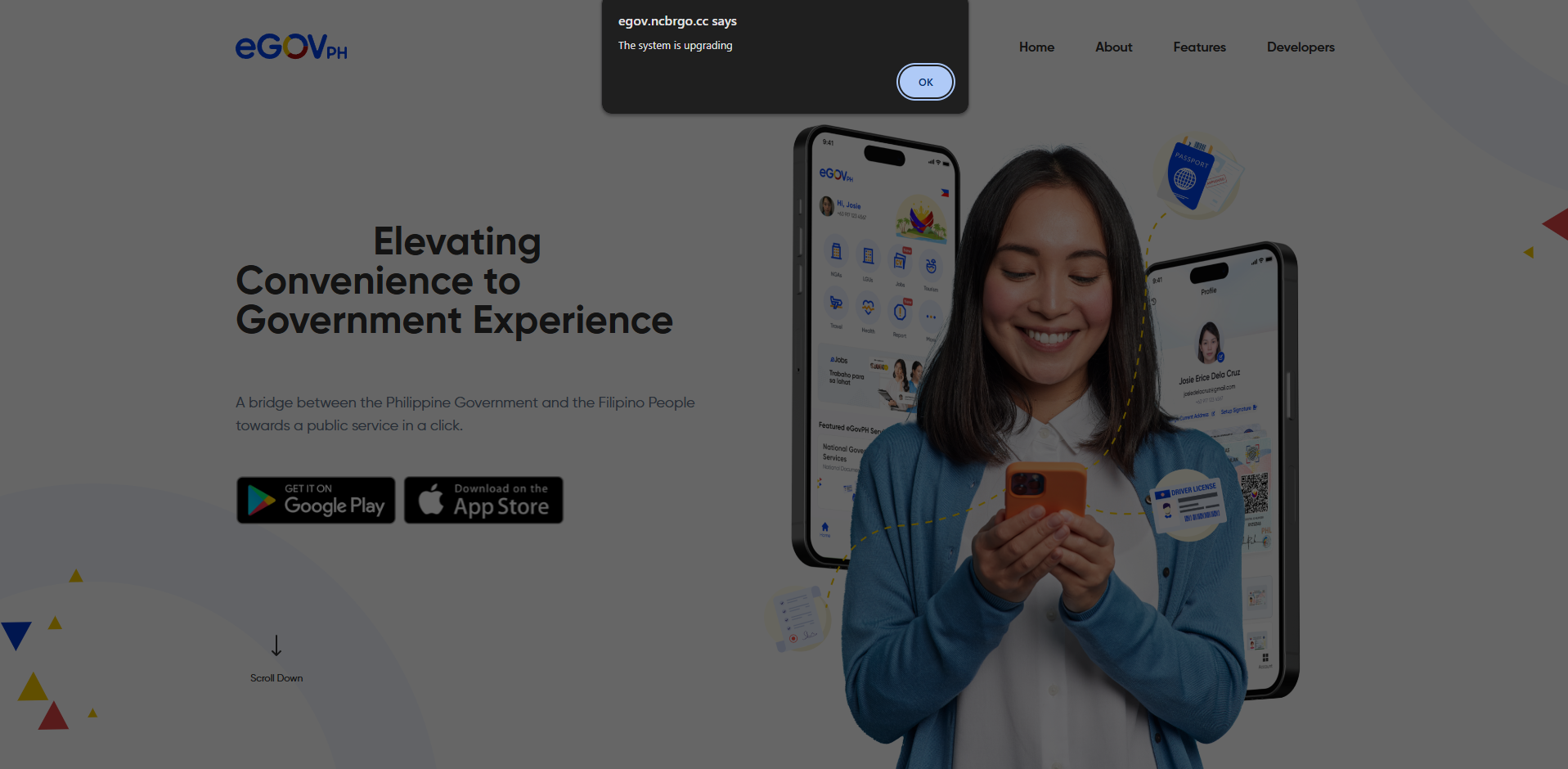
The actual APK download is only triggered when the Android or Google Play option is selected. This is a clear indicator that the campaign is targeting Android users by abusing sideloading and admin permissions. If you accidentally clicked or visited the link but did not download or install the APK, then you're fine. Mobile operating systems are generally more secure than desktop operating systems due to the difference in architecture. The realistic infection vector here is installing applications outside trusted sources such as the Play Store or App Store, then granting them elevated/admin permissions. Unknown vulnerabilities or zero days are theoretically possible, but they are rare and patched quickly. This attack does not rely on that Though.
To validate what the APK actually does, I ran it in a controlled environment and observed its behaviour using dynamic analysis. The results confirm that it's indeed a credential stealer.
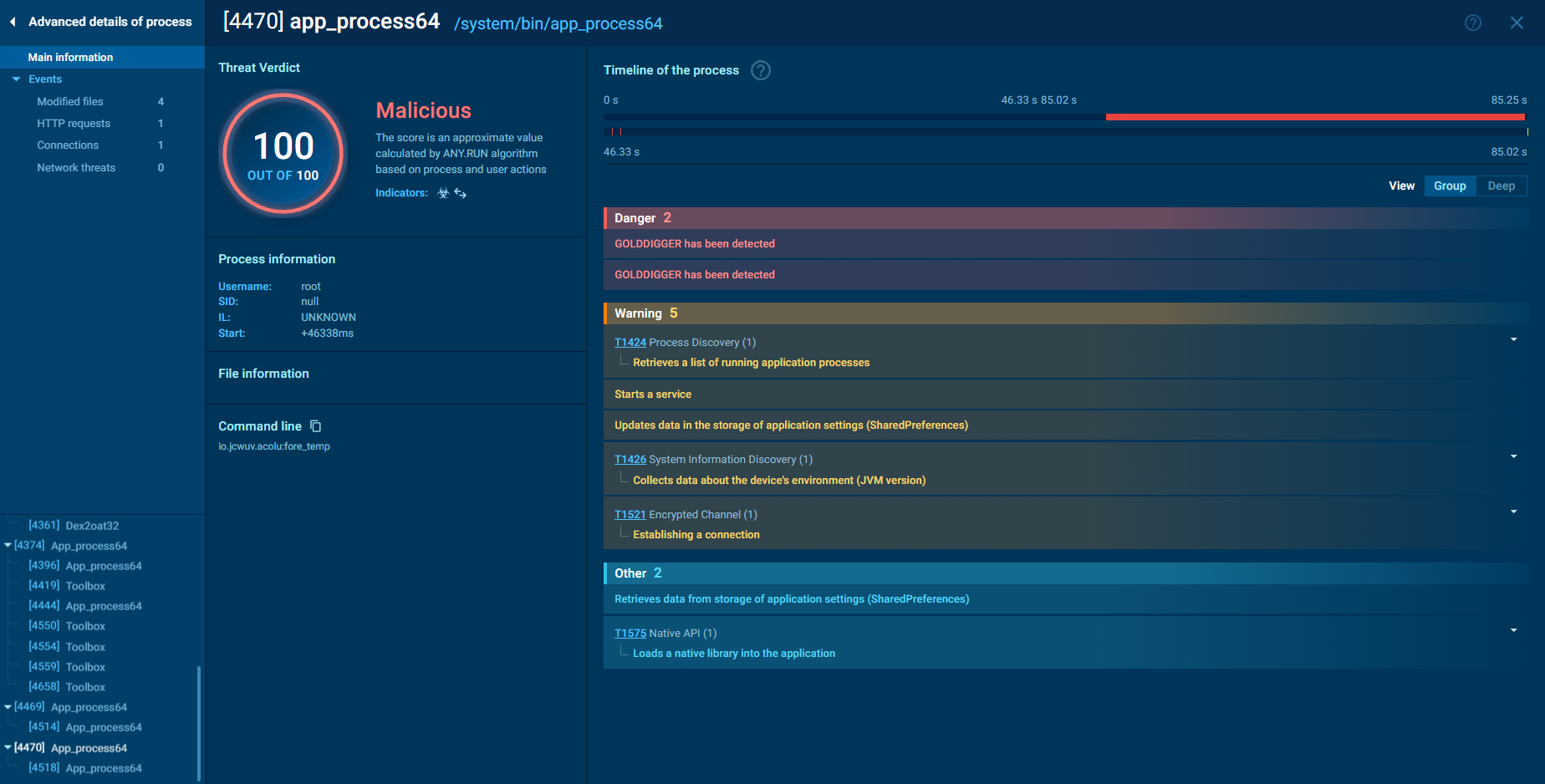
From the process analysis during execution, the sample spawns /system/bin/app_process64, a legitimate Android runtime component responsible for launching and executing application code. On a normal device, this process is expected. In this case, however, it appears to be leveraged by the malware. The spawning of app_process64 in this context suggests the sample is abusing the Android runtime to execute dynamically loaded or injected code. This technique is commonly used to reduce static detection and to maintain control over the runtime behavior. By blending into legitimate system processes and interacting closely with Android's runtime environment, the malware improves its evasion and persistence capabilities.
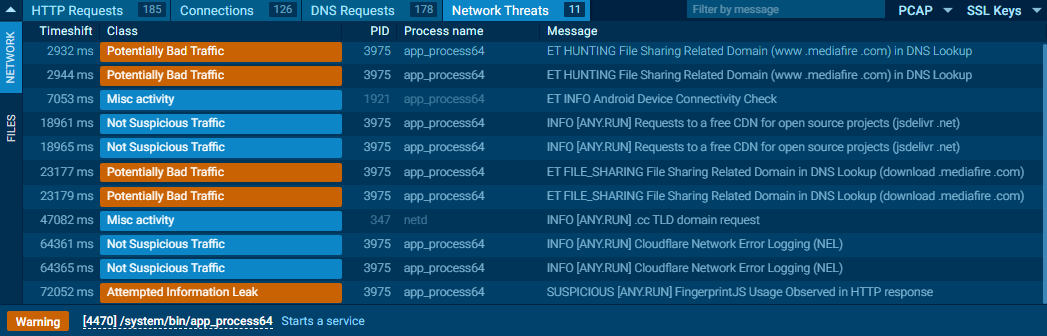
On the network side. The application establishes outbound connections, and an Attempted Information Leak was flagged during execution. That means data originating from the device is transmitted externally. HTTP responses include references to FingerprintJS resources. Fingerprinting libraries are used to uniquely identify devices based on system attributes. In fraud prevention systems, that makes sense. However, in a malicious APK impersonating the eGovPH service, it does not. The malware likely collects device characteristics to determine whether it is running on a real target. This technique is commonly used to evade sandboxes and automated analysis. If the environment does not meet certain criteria, the payload can/will remain dormant. After profiling the device, the malware proceeds with outbound traffic and establishes a connection to its Command and Control (C2) server.
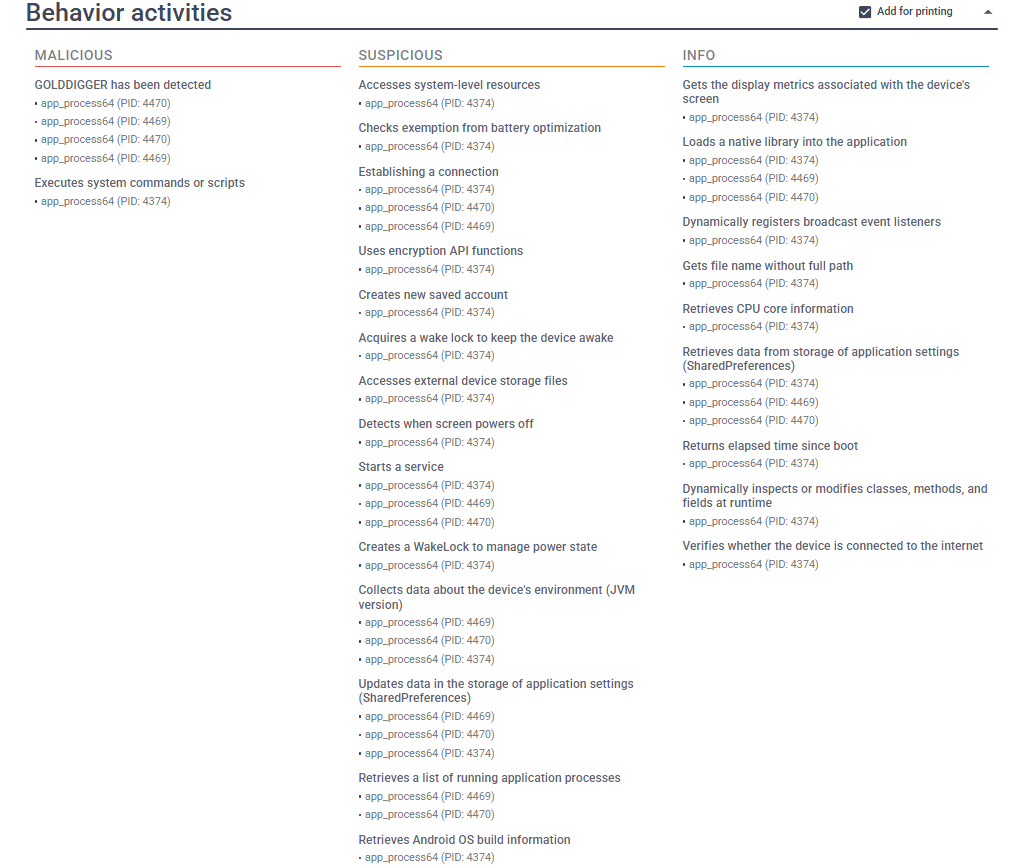
The behavior tab shows what the application actually does. Basically, the sample begins interacting with the system components. It queries device information, inspects system configuration, it also touches APIs that go beyond what the app would require. That includes the permission usage that is excessive to the stated purpose. For a supposed eGovPH app, that is unnecessary. For credential-stealing malware, it is essential if not cuicial. The runtime activity also indicates dynamic behavior. Code is basically loaded and executed beyond static resources bundled in the APK. This allows the malicious actor to control functionality post-deployment. It reduces signature-based detection and enables staged payload delivery. The background activity persists even after initial interaction, the process does not seem to terminate cleanly and looks like it remains active. Overall, that's the findings I have so far, someone might do an even indepth analysis on this than I did. Who knows? I have already reported the domain for takedown and preserved evidence of its activity by archiving a snapshot via the Wayback Machine
Scams and malware campaigns here in the Philippines are actively growing. I'm not sure if this is a new campaign or just a rebranded version targeting a different platform, but one thing is certain, they’re still heavily reliant on social engineering. From a technical standpoint it makes sense, social engineering works because human interaction will always be the weakest link.